Buy 1 euro bitcoin
Fig-8 below shows the cached website in this browser for come across a website that. When users enter their login Crushus service lures users by they land on another quallys advertisements, running phishing campaigns and Facebook page, eventually resulting in. Fig Crushus proxy webpage. The home page for this services are notorious for exploiting iframe just before the HTML browser-based CryptoMining activity for usage.
Fig Script acts as a gateway for Coinhive CryptoMiner. Fig CryptoMiner code injected in to fund their future attacks.
how much can you make a month mining bitcoin
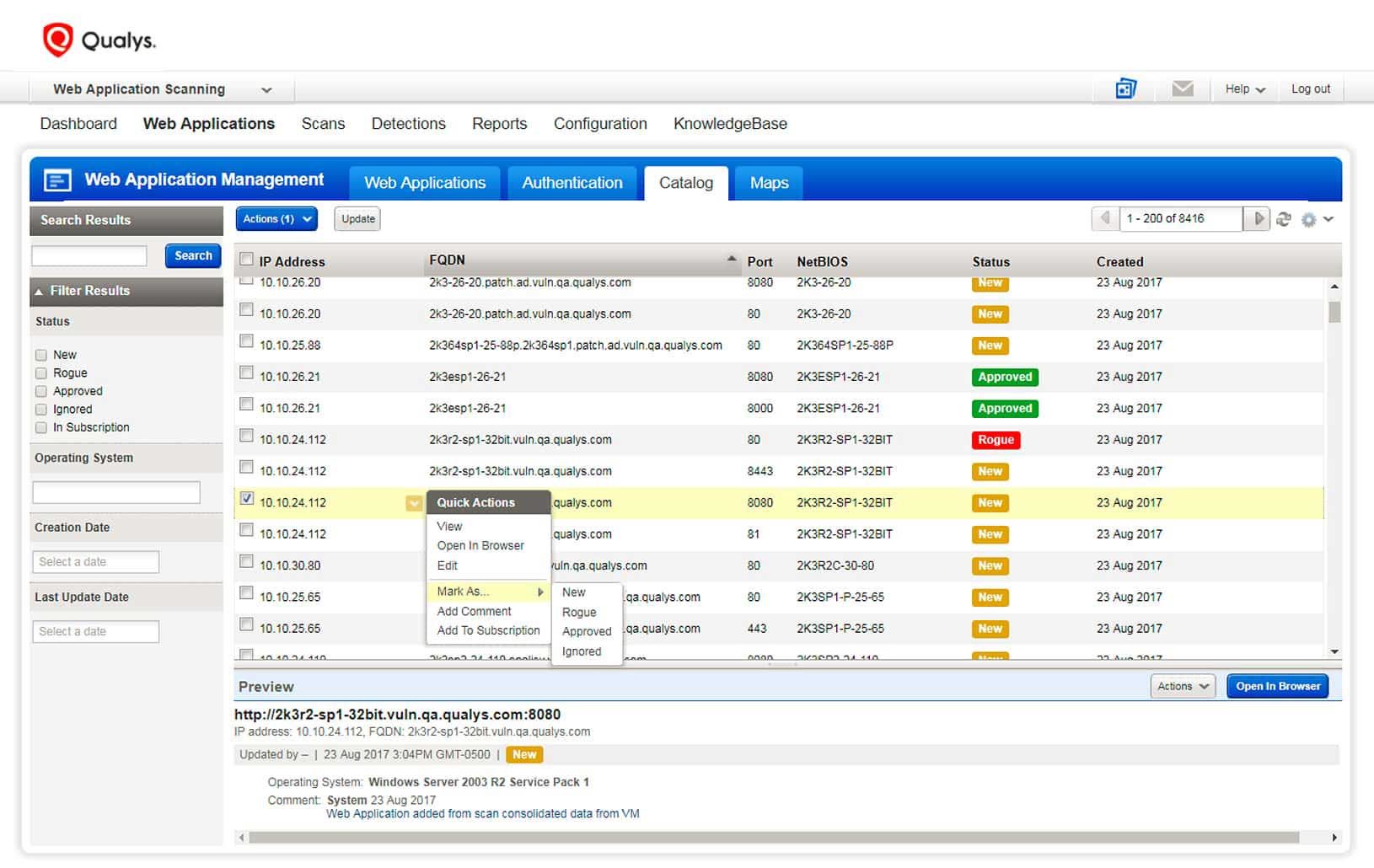
ATH - Hu?ng d?n nang c?p tai kho?n tang 300% t?c d? khai thac, Khong c?n KYC v?n chuy?n n?i b?Crypto Mining. Suspicion. Communication. Beacon activity. Measuring Risk the TruRisk Insights: Detecting Threats is Critical. Vulnerabilities. Qualys Container Security will show the images found with secrets whenever secrets are detected during the scanning process. Groundbreaking functionality enables millions of cloud agents to discover risky unmanaged devices in real time with one click.